Owasp File for Testing File Upload Validation
Unrestricted File Upload
What is Unrestricted File Upload Testing and how to test for Unrestricted File Upload Vulnerabilities including filter bypass techniques for Windows, Linux, Apache and IIS.
What is Unrestricted File Upload?
Vulnerable upload functions allow attackers to bypass input controls, upload payloads and potentially perform control execution
Spider web application file upload functions that practice non have the correct controls in place to ensure user uploaded files are validated or sanitised are potentially vulnerable to unrestricted file upload. This certificate outlines the testing process for file upload functions while performing a penetration test. This document contains various techniques to bypass File Upload Black List filtering and concludes with a helpful check list.
Identify File Upload Functions
File upload functions are both easy to place and piece of cake to exploit. Typical places are profile paradigm avatars, document upload functions and file import functions. Burp passive scanner will identify file upload entry points when you're at the discovery and application mapping phase.
Looking for a manual web app penetration test? See our web application pen testing page for more details
Using Burp Intruder to Test for Unrestricted File Upload
Web applications often utilize black listing for file input validation or sanitisation which is normally insufficient. If a file extension is missed from the blacklist an attacker can bypassed filtering. The preferred mechanism for input validation is input white listing, which uses a denyall approach and only allows input that is required.
Burp Testing File Upload Extensions
- Manually upload a file that volition likely fail the upload validation or sanitisation exam, find a response that can exist used to identify the web awarding is rejecting the file extension.
- Send the upload request to Burp intruder
- Articulate the default insertion points
- Select the file extension point equally the insert location
- Select a payload containing various extensions php.jpg, asp.jpg etc
- In options configure grep within response to contain the failed response string identified at footstep 1
- Start intruder, whatever responses unticked for the grep string are likely vulnerable are require farther inspection and Confirm any findings
Key Points:
- Exam all extensions using Burp Intruder and use the Grep feature to sort results
- Use uncommon file extensions that may bypass the black list such as:
.php3,.php5,.phtml
Test for File Upload Content-Type change with Burp
Identify accepted file upload Content-Type'due south accepted by the target.
- Establish a baseline – utilize a known accepted Content-Type and monitor the applications response, repeat with a content type that is likely not accepted, use the failed response at footstep 6
- Send the upload request to Burp intruder
- Clear the default insertion points
- Select the "Content-Type:" header as the insert location
- Select a payload list containing Content-Types
- In options configure grep within response to contain the failed response string identified at step i
- Start intruder, any responses unticked for the grep string are likely vulnerable are require farther inspection
Confirm any findings
Central Points:
- Examination all Content-Types using Burp Intruder and utilise the Grep feature to sort results
- Endeavor irresolute the Content-Type to ane that is supported, with a extension that the web server / web app will process
- Effort uncommon Content-Types that may bypass the black listing
File Proper noun and Extension Fuzzing
The file name and extension should be tested for input validation, what happens if the file name is an XSS, SQLi, LDAP or a Control Injection payload?
- Manually upload a file that will probable neglect the upload sanitisation or validation test, notice a response that can exist used to identify the spider web application is rejecting the file extension
- Ship the upload request to Burp intruder
- Clear the default insertion points
- Select the file extension or file proper name indicate every bit the insert location
- Select a payload containing various injection [js, XSS, CMD, LDAP, Xpath, SQL etc [ payloads
- In options configure grep inside response to contain the failed response string identified at step 1
- Start intruder, any responses unticked for the grep cord are likely vulnerable
- Confirm findings
File Upload Black Listing Featherbed Techniques
Windows IIS Server Black List File Upload Bypass:
- Upload a file with the semi colon after the black listed extension, such as:
shell.asp;.jpg - Upload a directory with the .asp extension, then name the script within the directory with a permitted file extension, case:
folder.asp\file.txt - When serving PHP via IIS
< > and .get converted dorsum to? * . - Use characters that can supervene upon files, instance
>>tin can replaceweb.config - Endeavour using spaces or dots afterward characters, example:
foo.asp..... .. . . . -
file.asax:.jpg - Attempt to disembalm information in an error message past uploading a file with forbidden characters inside the filename such as:
| %< * ? "
Apache Windows Black List Bypass:
- Windows 8.3 characteristic allows short names to replace existing files, example: spider web.config could be replaced by web~config.con or .htaccess could be replaced past HTACCE~i
- Attempt to upload a . file, if the upload function root is
/www/uploads/it will create a file called uploads in the directory above.
Looking for a manual consultant atomic number 82 spider web awarding security test? Run into our web application penetration testing services page for more details
Full general Black Listing Bypass:
- Identify what characters are beingness filtered – use burp intruder to appraise the insert points with a meta graphic symbol list
- Ensure your list contains uncommon file extension types such as
.php5,.php3,.phtml - Test for flaws in the protection mechanism, if information technology's stripping file names can this be abused? Example:
vanquish.p.phppif the app strips .php it could rename the extension back to .php - Try a naught byte
%00at various places within the file name, case:shell.php%00.jpg,shell.php%0delete0.jpg– detect how the application responds - Double extensions: if the application is stripping or renaming the extension – What happens if you lot give information technology two extensions? Example:
vanquish.php.phpor 4shell.txt.jpg.png.asp - Try long file names, case
supermassivelongfileeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeename.phpapply other filter bypass techniques used in conjunction with long file names - Try
test.asp\,test.asp.\ - Can you upload the wink XSS payload, that is named as a .jpg
- Try the previous technique but use PDF or Silverlight instead
- Same over again just endeavor to abuse crossdomain.xml or clientaccesspolicy.xml files
- Try using encoding to bypass blacklist filters, try URL, HTML, Unicode and double encoding
- Combine all of the above bypass techniques
- Try using an alternative HTTP Verb, try using Mail instead of PUT or Become (or vice versa), y'all can enumerate the options using Burp Intruder and the HTTP Verbs payload list
- Additionally, ensure all input points are fuzzed for diverse input validation failures such as, XSS, Command Injection, XPath, SQLi, LDAPi, SSJI
Bypassing File Upload White Listing
- Enumerate whitelist and test for whatever permitted file extensions that tin be driveling
- Test files contents are existence validated
- Test that extension renaming techniques such equally
shell.php.pngare not possible
Bypass File Size Upload Mechanisms
Malicious File Contents
Assess whatever file upload contents is correctly sanitised past the application. For case, can you inject XSS into an Excel, CSV or txt files that will later exist rendered by the application? Utilize Burp repeater and intruder to effort injecting various payloads within file import and upload functionality, assess the applications response.
EXIF Image Data
Can a reverse shell be injected inside epitome EXIF data ?
Install on Kali:
apt-get install exiftool
After injecting the code within the prototype file, only upload the file and verify the file is the same using a checksum (details below).
Looking for a transmission consultant lead mobile application security test? See our mobile application penetration testing services folio for more details
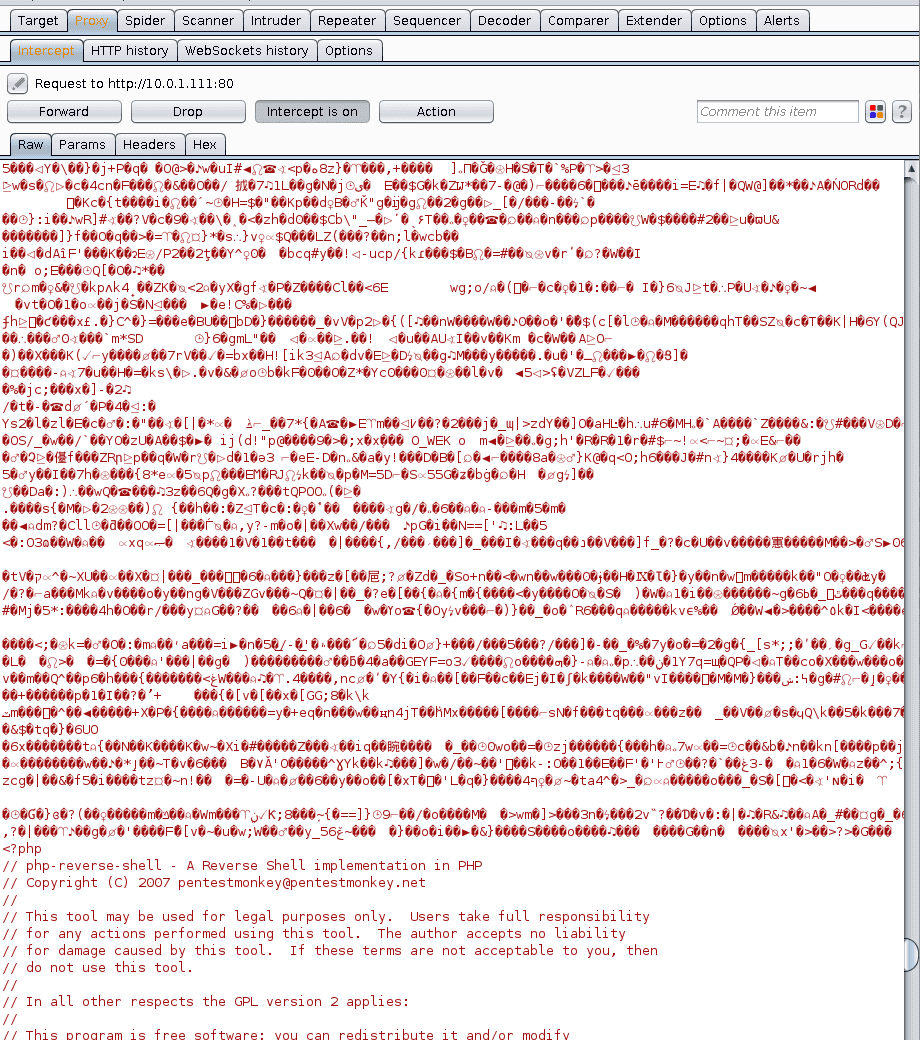
Injecting into the asking with Burp
This is a similar technique to the EXIF method in a higher place, yet you paste the lawmaking direct into the burp asking.
- Upload a legitimate epitome using burp and verify upload is successful
- Send the previous request to burp repeater
- After the legitimate image data in the asking, endeavour to inject payloads (injection payloads or a reverse shell)
- Submit the request
- Download the uploaded file from the target server, verify it has the independent payload within, can you leverage this to execute a payload on the target server?
Verify the file is Uploaded
Regardless of the method you used in the previous step (EXIF or Modifying the Burp Request) create a checksum of the file locally and upload to the target, download the file from the target and verify the checksum matches.
Key Points:
- Checksum a file, upload it to the app, download it from the app, verify it'south the aforementioned file
Techniques for Server Side Control Execution
If it's possible to successfully upload a trounce to the target web application you lot tin attempt some of the following techniques to execute the uploaded shell.
Has your organisation performed an External Pen Test recently? See our Network Penetration Testing services page for more details
- Apache MIME Types: Attempt to upload a renamed file east.g.
vanquish.php.jpgorshell.asp;.jpgand assess if the web server process the file by exploiting weak Apache MIME types - Null Byte: Endeavour a cypher byte
%00at the end of the file name or within such as:shell.php%0delete0.jpg– discover how the awarding responds - Tin can y'all upload dot files, if and then can you lot upload a .htaccess file an abuse AddType:
AddType application/x-httpd-php .foo - Exist mindful of whatsoever processing to upload files – Case: Could command injection be used inside a file proper name that will later be candy by a backend backup script?
- Be mindful of whatever server side processing to upload files – If compressed files are permitted, does the application extract them or vice versa?
- Does the server Anti Virus procedure uploaded files? – Try uploading a compressed file type such every bit .zip, .rar etc if the server side AV is vulnerable, information technology's possible to exploit and gain control execution.
Unauthenticated File Upload Testing
Unauthenticated file upload, allows an attacker to DoS a target by fill deejay space on target machine.
Testing for Capricious File Upload using Burp:
- Place file upload function
- Perform a normal file upload using an authenticated user (if possible)
- Transport the asking to burp comparer
- Remove the cookie or session identifier from the asking
- View the response to assess if file upload is possible without hallmark
Has your system performed a Vulnerability Cess recently? Meet our Vulnerability Testing services page for more than details
Testing for DoS Condition Disk Filling
If within testing scope, assess if DoS is possible via file upload or disk filling from a unmarried session. Use a low number (~100) of jpg files and use Burp intruder Number payload pick to increment the payload names, e.g. image1.jpg, image2.jg, image4.jpg etc.
Large File Upload
Upload a large file and appraise if the application allows the upload.
If shell admission is available on the exam, information technology'due south easier to perform a server side assessment checking for LimitRequestBody within the Apache config and MAX_FILE_SIZE within php.ini
Test for Server Side Antivirus Scanning
Utilize an EICAR file, a benign test file for testing AV detection and verify it gets detected by AV scanners on VirusTotal.
- Checksum the EICAR file
- Perform a normal file upload
- Download the EICAR file
- Checksum the EICAR file and validate it's the same file
Repeat the aforementioned test 24 hours later and assess if any daily antivirus filtering is taking place.
CSV Macro Injection
If the awarding has an consign function assess if it'southward possible to injection macros within the web application that could be executed client side by another user.
Example:
- Assailant injects malicious payload within the spider web application
- Administrator logs in and exports the web application data to CSV
- Attackers injected payload is then executed client side past the victims Excel, it'due south likely even if excel prompts or warns the victim will keep every bit the exported data is from a site they trust.
Key Points:
- Upload a malicious payload and access if information technology'due south possible to download the payload from a back finish interface.
- Verify the payload is the same file using a checksum
File Upload Testing Check Listing
Discovery:
- Identify File Upload Points
Windows IIS Server Black List File Upload Bypass:
- Upload a file with the semi colon afterwards the black listed extension, such as:
shell.asp;.jpg - Upload a directory with the .asp extension, and then name the script within the directory with a permitted file extension, example:
folder.asp\file.txt - When serving PHP via IIS
> < and .become converted back to? * . - Use characters that tin supercede files, example
<<can replaceweb.config - Try using spaces or dots after characters, instance:
foo.asp..... .. . . . -
file.asax:.jpg - Endeavour to disclose information in an error message by uploading a file with forbidden characters inside the filename such as:
| > < * ?"
Apache Windows Black List Bypass:
- Windows eight.three feature allows brusk names to supercede existing files, instance: web.config could be replaced past web~config.con or .htaccess could be replaced past HTACCE~1
- Attempt to upload a . file, if the upload function root is
/www/uploads/it will create a file called uploads in the directory above.
General Black List Bypass:
- Place what characters are being filtered – utilize burp intruder to assess the insert points with a meta grapheme listing
- Ensure your list contains uncommon file extension types such equally
.php5,.php3,.phtml - Exam for flaws in the protection mechanism, if it'southward stripping file names can this be driveling? Example:
crush.p.phppif the app strips .php it could rename the extension back to .php - Endeavour a nix byte
%00at various places within the file name, example:vanquish.php%00.jpg,beat out.php%0delete0.jpg– observe how the awarding responds - Double extensions: if the application is stripping or renaming the extension – What happens if you requite it 2 extensions? Example:
shell.php.phpor 4beat.txt.jpg.png.asp - Try long file names, instance,
supermassivelongfileeeeeeeeeeeeeeeeeeeeeeeeeeeeeeeename.phpapply other filter bypass techniques used in conjunction with long file names - Endeavour
test.asp\,test.asp.\ - Can you upload the wink XSS payload, that is named every bit a .jpg
- Effort the previous technique but utilize PDF or Silverlight instead
- Same again but attempt to corruption crossdomain.xml or clientaccesspolicy.xml files
- Try using encoding to featherbed blacklist filters, try URL, HTML, Unicode and double encoding
- Combine all of the higher up featherbed techniques
- Endeavour using an culling HTTP Verb, endeavour using POST instead of PUT or GET (or vice versa), you can enumerate the options using Burp Intruder and the HTTP Verbs payload list
- Additionally, ensure all input points are fuzzed for various input validation failures such as, XSS, Command Injection, XPath, SQLi, LDAPi, SSJI
Bypassing File Size Upload Checks:
- Use EXIF prototype file technique
- Inject vanquish directly subsequently image data inside Burp request
- Verify uploaded file is the aforementioned using checksums
Techniques for Executing Uploaded Shells:
- Apache MIME Types: Attempt to upload a renamed file due east.yard.
beat out.php.jpgorshell.asp;.jpgand assess if the web server process the file by exploiting weak Apache MIME types - Null Byte: Try a null byte
%00at the end of the file name or within such as:shell.php%0delete0.jpg– observe how the application responds - Can yous upload dot files, if so tin can you upload a .htaccess file an corruption AddType:
AddType awarding/x-httpd-php .foo - Be mindful of any processing to upload files – Example: Could command injection be used inside a file name that will after be processed by a backend backup script?
- Exist mindful of any processing to upload files – If compressed files are permitted, does the awarding excerpt them or vice versa?
File Upload DoS Testing:
- Unauthenticated File Upload Testing
- Testing for DoS condition Disk Filling
- Large File Upload
Test for Server Side Anti-Virus:
- Checksum the EICAR file
- Upload & download the file, verify the checksum matches original
- Repeat test in 24 hours
CSV Macro Injection:
- Test for CSV macro Injection
FAQ
A local file upload vulnerability where an application fails to verify the contents of an uploaded file, allows an attacker to upload a malicious file to the web server or application. Malicious files such as reverse shells, malware or viruses could potentially be executed or stored / served by the vulnerable application.
- Do Not Shop Uploaded Files Within The File Organisation: Avoid storing files direct inside the webserver file arrangement, to avoid execution consider storing uploaded files within a database or segregate the uploaded files on another server.
- Sanitise File Names: rename sanitise and encode uploaded file names before storing or reflecting inside the spider web awarding.
- Verify Whitelisted File Types: Ensure uploaded fille types are whitelisted and the whitelist of canonical file types is validated to avert malicious attacks to spoof or evade filtering.
- Server-side Anti-Virus: Ensure server-side anti-virus is in place and configured to scan uploaded files.
The potential risks of an unrestricted file upload vulnerability depends on the level of exploitation reached. Typically, successful exploitation of a file upload vulnerability results in a compromise the target host which could, given the correct fix of circumstances event in an adversary uploading malicious payload to the server such as a reverse vanquish and successfully gaining shell level admission to the server; potentially exposing sensitive/personal data which could be modified or deleted. If an aggressor were to gain vanquish level access to the server this could exist used every bit a potential betoken to launch a lateral move and penetrate deeper into the network. Other attacks such as DoS assail, or using the server to store and distribute viruses or malware could too be executed. Typically, it depends on how the target application handles the uploaded files, and how well the uploaded files are restricted from the residuum of the network and what controls be to prevent malicious files from being uploaded, and/or executed.
jacobsennoeve1936.blogspot.com
Source: https://www.aptive.co.uk/blog/unrestricted-file-upload-testing/
0 Response to "Owasp File for Testing File Upload Validation"
Post a Comment